Database encryption is considere to the foundation of information technology security. Enterprises databases are now goldmines for businesses, which provide information on demand and valuable insights for business decision-making. Databases now consist of confidential and competitive information, which is considere the intellectual property of each enterprise.
A typical business database may contain basic customer demographics to the most confidential financial information. Loss of data or stolen data may result in tampering with a business’s brand image and may cause many competitive disadvantages. In case of high-profile data breaches, the organization may find it difficult to survive further. You need to carefully consider your specific requirements. Based on that make an accurate selection and enjoy the best features out of it.
As database security is one of the top priorities of any given enterprise, it is important to mitigate all the risk factors related to database management and comply with existing and upcoming data security regulations. Database encryption is not there by default in DBMS, but it is considered one of the essentials in database security in the open and sophisticated IT environment.
Is encryption a choice or necessity?
Table of Contents
As the corporate networks are becoming more global and open now to accommodate a greater number of customers, providers, vendors, partners, and industry experts, data encryption becomes a mandate than a choice. As the experts point it out, encryption is consider the last line of defense. When it comes to database security encryption, it covers the data stored within a database and the data backups.
With proper encryption, data sets will remain fully protected even in case of a data breach. The modern technological approaches to data encryption make it much easier for organizations to deploy better database encryption practices. Another reassuring factor in favor of data encryption is that it does not demand any changes in the existing database applications.
While considering data encryption, it is also important to get a reliable and expert consultant to do it by meeting the standards. For this, you need first to understand your exact requirements based on the nature of data and the volume of data you have to handle. For this, you have to distinguish between critical and non-critical data and identify which must protect through data encryption and whatnot.
Encryption surely comes at a cost, and so it important for you to decide by considering the cost elements also into consideration. To make a viable decision in terms of data encryption, you may consider various aspects of implementing encryption and running. The providers like remote DBA can offer you expert service support in managed database administration and data protection like encryption and other industry standards.
Pros and cons of Database encryption
As with any other technology, data encryption also has some pros and cons associated with it. Even though the benefits outweigh the shortfalls, encryption needs to be done by carefully considering it. Enterprises should consider all these aspects to make a well-informed decision about implementing data encryption on their enterprise systems.
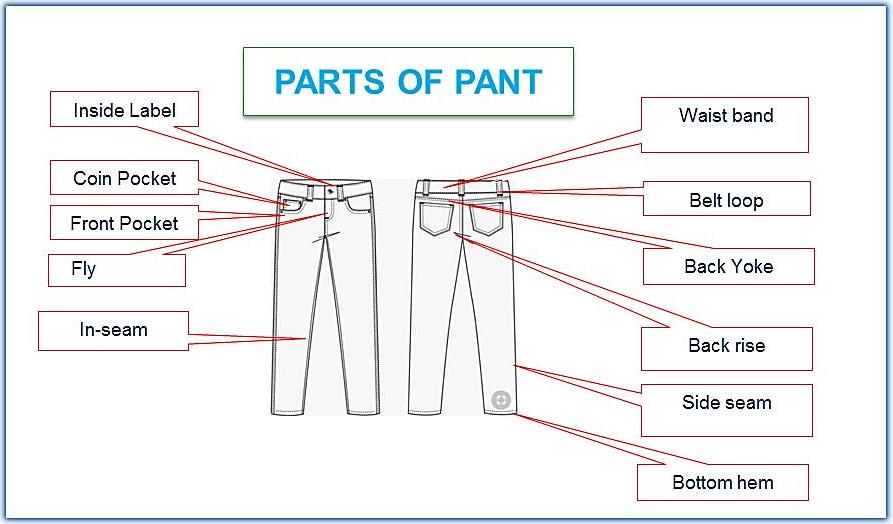
Process of Database encryption
- Avoiding data breaches: Data Encryption will help avoid any inherent risks of data breaches and provide optimum protection to data as intellectual property and various other associated information enterprises may hold.
- Ensuring better security practices: As encryption is performe on the same set of data itself. The information is well protected irrespective of how data transmission is done. This will add a layer to the data security of enterprises.
- Data confidentiality: Organizations are need to many confidentiality obligations related to critical and sensitive data. HIPAA and other such governmental regulations make data confidentiality a mandate during online transactions in the healthcare, financial, and many other sectors.
With proper data encryption, you can read the data only by the intended recipient, who holds the key to open and read the data. This makes enterprises complain about data confidentiality policies and practices.
Cons of database encryption
Along with the process of database encryption, there come some disadvantages too. Which enterprises need to consider to ensure optimum data protection.
- Encryption key: There is no doubt that data encryption is an impressive task for technology experts to accomplish. The greater number of data encryption keys out there, the most difficult its management tasks will become. It is also not an easy task to maintain all encryption keys. If any key to encryption is lost, then the data associate with it may also imply loss.
- Cost: Data encryption is proving to fairly high-price as the systems. Which keep the data encryption need to have a higher capacity. It also demands frequent upgrades to perform the encryption and decryption tasks successfully. With compromised systems, the operational efficiency of encryption may also deteriorate significantly. So, to facilitate encryption, there is a considered cost upfront for enterprises. There are add-on costs too to maintain it properly.
- Compatibility: Encryption technologies very complicate while trying to learn them with existing programs and applications. This may have a negative impact on the routine IT operations existing in the system.
Enterprise databases manage a wide range and a high-volume of sensitive business data. In light of the need for better security, database encryption should undoubtedly be one of the major priorities for organizations of all types and sizes. With the intention to protect their valuable data assets. However, encryption needs to accomplished by following the industry best practices to ensure optimum security levels and top-notch key management.
Final Word
Suppose the enterprises follow these best practices we discussed here in encryption. In that case, they may find a good return on investment on the go as it will fully protect. The most sensitive information for the company and its credibility. In many applications and industries, these encryption standards also may comply with industry and government regulations. The further prevent the possibility of any data breaches. It will also help protect the reputation and corporate brand of enterprises.